Bug bounty
Introduction
While we do our best to ensure that Manalyze is secure, we know that things go wrong from time to time. For this reason, we welcome your help in identifying possible flaws in the program and on this website, provided you do this in an ethical way and report your findings to the maintainers of this project.Rules
- The bounty for bugs is set to 100€, payable by wire transfer or Bitcoins. You may also opt for a donation to the charity of your choosing.
- Current budget remaining for the bug bounty: 300€. The bounty will be temporarily suspended when the funds allocated to it reach zero.
- Crashes in Manalyze are eligible as long as they occur in code written by Manalyze's team. Bugs which can be traced back to third party code (i.e. YARA, OpenSSL...) are welcome and will be forwarded to their rightful recipients, but will not receive any compensation unless said library has been blatantly misused by Manalyze's maintainers.
- All bug reports must be accompanied by relevant PE files causing the crash.
- Attack scenarios involving malicious plugins are out of the scope: if the prerequisite for the attack is that someone can drop a DLL file on the victim's system, they probably don't need to exploit Manalyze to get remote code execution. For this reason, these types of attacks were not taken into account in the application's threat model.
- Researchers don't have to prove that the bug is exploitable. As long as Manalyze crashes, the bug is eligible (provided the conditions mentioned above are met).
- Security issues in the
manalyzer.orgmachine are eligible as well. However, only bugs which have an actual security impact will be rewarded with money (i.e. exploitability needs to be demonstrated). In particular, vulnerabilities commonly used to extort money from gullible clients or otherwise fill empty pentest reports (missing clickjacking headers, XSS on logout forms, etc.) will be ignored. You know what these are. - Please do your best not to DoS this website.
- Manalyze's maintainers ultimately decide which bugs are awarded with money and this decision cannot be appealed.
- A maximum of two bounties will be awarded per person. In case we need a little time to pay up, please keep in mind that the money comes out of our personal bank accounts. It's not that we don't want to hear about your third and fourth bugs — it's that we don't want to get broke even more.
Hall of Fame
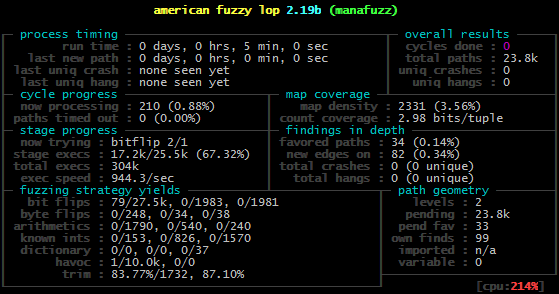
Fuzzing Manalyze
This section contains instructions you can follow if you intend to fuzz Manalyze. In this example, lcamtuf's AFL is used and the fuzzing effort is focused on the PE parser. The following lines indicate how to get the latest version of Manalyze and build a minimal executable to fuzz:mkdir manafuzz
git clone https://github.com/JusticeRage/Manalyze.git
cp -r Manalyze/manape/ Manalyze/include/manape/ manafuzz
cd manafuzz
cat >main.cpp <<EOF
#include "manape/pe.h"
int main(int argc, char** argv)
{
if (argc < 2) {
return -1;
}
mana::PE pe(argv[1]);
if (pe.is_valid()) {
return 1;
}
else {
return 0;
}
}
EOF
afl-g++ main.cpp manape/*.cpp -lboost_system -lboost_regex -I. -std=c++11 -o manafuzzmain.cpp to call any additional function you want to fuzz: all this example does is load a PE file and parse it, before exiting.The next step is to gather some PE executables which will be used as input files. Options include the handcrafted PEs from the Corkami project, as well as the files used by Foxglove to fuzz ClamAV. Assuming you put these input files in a folder called
input/ and want to save the results in a folder called output/, use the following command to launch AFL:
afl-fuzz -m500 -i input/ -o output/ -t100 -- manafuzz @@